The quantum era is upon us as the goliaths of the 21st century lock horns in their stake for...
Read MoreQuantum Computing: Tiny Machines, Monumental Impacts
The quantum era is upon us as the goliaths of the 21st century lock horns in their stake for quantum supremacy. Leading the charge, Google recently unveiled Willow, a cutting-edge quantum computing chip that achieves a groundbreaking reduction in errors solving a 30 year old challenge. In benchmark tests, Willow completed a standard computation in under five minutes, a task so complex it would take the world’s most powerful supercomputer over 10^25 years, far beyond the age of the universe.
At its core, quantum computers leverage the strange fundamental properties of subatomic particles such as entanglement and superposition with the ability to perform computations far beyond the realm of classical computers. While classical computers use bits (0s and 1s), quantum computers use qubits, which can exist in multiple states simultaneously. This unique property allows quantum computers to solve certain types of problems exponentially faster than classical computers.
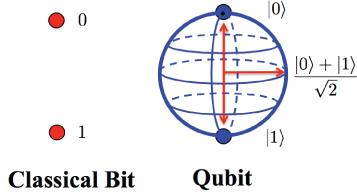
Fig 1: Bits vs Qubits
Quantum computing is set to revolutionize various fields of technology such as artificial intelligence, supply chain optimization, complex molecular simulations for drug discovery, and improve climate modeling. Beyond these practical applications, quantum computing is being envisioned as a tool to comprehend the true nature of reality as they can the behaviour of fundamental particles to a high degree of accuracy. But perhaps their most profound and alarming impact lies in the realm of cryptography and security. The digital world relies heavily on cryptographic systems such as RSA and ECC to ensure security of communication channels, safeguard sensitive data and protect financial systems.These encryption standards leverage the fact that factoring very large numbers is resource heavy and time consuming for classical computers. However, these systems are not designed to withstand the capabilities of quantum algorithms like Shor’s, leaving them vulnerable in a post-quantum world. The Shor’s algorithm can efficiently solve problems like integer factorization and discrete logarithms. This threatens the security of widely used protocols such as RSA and ECC, posing a serious threat to encryption. While symmetric encryption schemes like AES (Advanced Encryption Standard) are less vulnerable to quantum attacks, Grover’s algorithm (another quantum algorithm) reduces the effective key length by half, necessitating longer keys to maintain security, hence requiring more computing power.
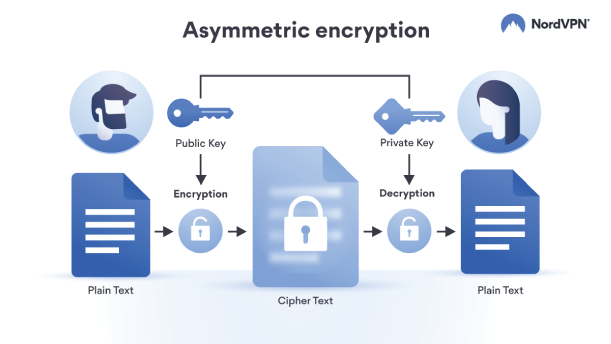
Fig 2: Modern day encryption
To address the looming threat that these new computers pose, researchers around the world are working on post-quantum cryptographic protocols that rely on problems believed to be hard for both classical and quantum computers. These include lattice-based, hash-based, code-based, and isogeny-based algorithms. Among these, lattice-based cryptography is one of the most promising approaches due to its efficiency and strong security guarantees. Most researchers also advocate for interim standard solutions that combine classic and post quantum cryptography(PQC) standards during transition. Organizations like NIST are working to standardize quantum-safe algorithms to replace RSA and ECC in the coming decades. Notable examples include CRYSTALS-Kyber for key exchange and CRYSTALS-Dilithium for digital signatures.
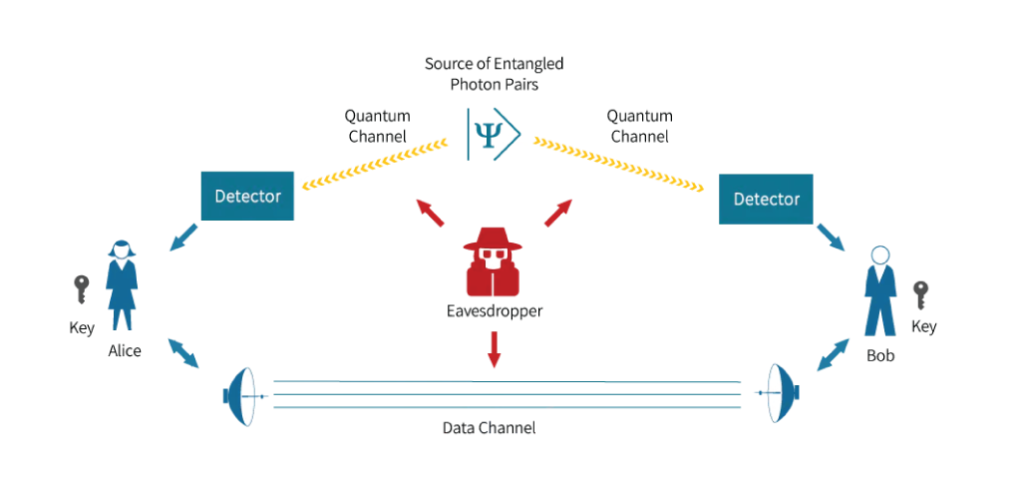
Fig 3: Quantum Encryption
As quantum computers advance, the threat of “harvest-now, decrypt-later” attacks looms larger. These attacks involve adversaries capturing encrypted data today, with the aim of decrypting it in the future when quantum computers gain the capability to break current cryptographic protocols. Encrypted data intercepted today could be stored and decrypted in the future, making immediate adoption of PQC a necessity for long-term security.
Beyond cryptography, the rise of quantum computing will influence geopolitics, economics, and innovation. Governments and industries must consider not only the technological implications but also the ethical challenges of deploying systems that could redefine privacy and security. The rise of quantum machines would be a landmark in technology, taking humanity to newer heights of innovation. While it poses a considerable threat to traditional cryptographic systems, it also offers the chance to innovate and strengthen digital security through post-quantum cryptography. By acting now, we can safeguard the future of our digital world against the inevitable quantum revolution.

Author Name
About the Author
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo. Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo. Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Services
Related Blogs
Enterprise Agility: What It Really Means for an IT Organisation
According to a recent Deloitte access survey, 80% of IT leaders believe that agility is essential...
Read MoreHow to Get Started on Your AI Journey: A Guide for Enterprises
AI holds the potential to unlock significant value by improving operational efficiencies...
Read MoreFive steps to a successful Jira Cloud Migration
Cygnus Consulting offers extensive experience and a refined methodology for migrating...
Read More



